Exec Summary: Last year this WordPress blog was hacked which led me to discover the timthumb vulnerability you may have heard of. I fixed timthumb and worked with Ben, the author to release timthumb 2.0. Then I started work on Wordfence, what I hope will be the best security plugin in the business for WordPress. Wordfence is now completing beta testing. Install it, it’s free and it will help protect your site and keep you off Google’s malware list and in the search results. For beginners: you install Wordfence by going to your WordPress blog’s “Plugins” menu, clicking “Add New” and searching for “Wordfence”.
Full Post:
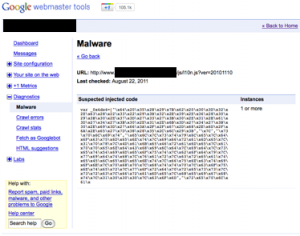
Last year on August 1, this WordPress blog was hacked. Thankfully I caught it quick enough to stay of Google’s malware list. I retraced the hacker’s steps and discovered a zero day vulnerability in many WordPress themes and plugins in the form of a popular image resizer called timthumb.php.
So I rewrote timthumb.php and worked with the author of timthumb and some of the WordPress team to merge my code into timthumb and we launched it as timthumb version 2.0.
But getting hacked made me realize that as awesome as WordPress is, it can do security better.
So I dropped everything and spent the last few months writing what I hope will be the last word in WordPress security.
A few days ago I quietly released Wordfence into the WordPress plugin repository. Since then I’ve been working with some amazing WordPress publishers to make Wordfence even better and I’ve been rapidly rolling out improvements, enhancements and (yes, believe it or not) a few bug fixes. I’d say Wordfence is getting close to finishing Beta testing at this point.
Except for two (rather minor) features, Wordfence is completely free. It is also backed up by a cluster of cloud based scanning servers that do most of the heavy lifting to keep your site running super fast.
Here are some of the more notable ways Wordfence enhances your WordPress security:
- Scans your core files against a reference copy which I maintain in our cloud servers.
- Lets you see what has changed, how the file has changed and even repair it.
- Scans your comments, posts and all files including core, themes, plugins and everything else under your WordPress root directory for malware, virus signatures, vulnerabilities and (very importantly) URL’s that are known to host malware or viruses.
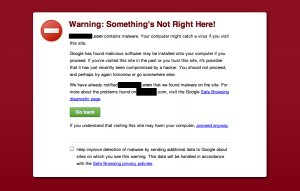
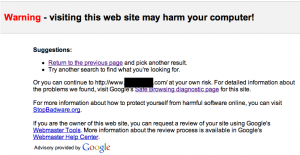
- I want to re-emphasize the last point. Wordfence keeps known dangerous URL’s, including ALL URL’s that are on Googles’ safe browsing list, out of your comments, pages, posts and files. This is by far my favorite feature because it’s virtually gauranteed to keep you off the dreaded red-page-of-death-malware-list that Chrome and Google use to ban sites.
- Wordfence comes with a complete firewall that lets you set up rules based on the type of traffic and either throttle or block offenders with an SEO safe 503 (come back later) HTTP message.
- Another favorite feature of mine is that you can block fake Google crawlers. I actually added this after I tested Wordfence on this site because I couldn’t believe how many scrapers were pretending to be Googlebot. So now they are all instantly blocked.
- Wordfence uses Google’s recommended reverse-forward DNS verification to sift the fake Googlebots from the real ones.
- It includes login security against every form of brute force attack out there including abusing your lost-password form.
- And what’s the point of having all this awesome security if you can’t see who is visiting, who’s getting blocked and what humans and robots are doing? So Wordfence includes real-time traffic that wait..for…it…
- …Includes crawlers, scrapers, robots and all non-human traffic. Something you can’t get from Google Analytics or any other Javascript based analytics package.
- I’ve even broken out Googlebot, other crawlers, 404 errors, humans and there’s an All Hits view.
- And of course it includes commercial grade city-level geolocation which is another feature that comes from our cloud servers.
- Wordfence is also built using much of the knowledge I’ve gained building Feedjit’s real-time analytics so it is careful to minimize any impact on network, website and mysql database performance and keep your website running super-fast.
Most importantly, Wordfence comes with a commercial license if you prefer first-class support and support forums for free users including a generic WordPress security forum where I’m happy to answer general config questions.
Improving WordPress security is going to be a marathon, not a sprint. I’m in this for the long haul. So check out Wordfence now by installing it on your blog and work with me to make the Web and WordPress more secure.