News [April 24th, 2012]: I’ve launched Wordfence to permanently fix your WordPress site’s security issues. Click here to learn more.
I just helped another target of the timthumb.php vulnerability to clean their machine. The method the hacker used to hide their tracks was a little different to what I’ve seen in the past. So I wanted to mention it here and let you know how to scan for it.
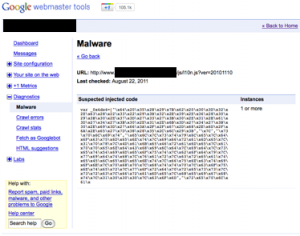
As I previously mentioned, the method I’ve seen hackers use to hide their source code is to encode it using base64 encoding and then use base64_decode and eval() in PHP to execute the code at runtime.
You can scan for base64 decoding by getting a shell on your WordPress server and running the following in the root of the WordPress installation directory:
grep -r base64_decode *
Keep in mind that some files that are not hacked will show up, like the newest version of timthumb.php which includes a base64 encoded image. But this is a good starting point to get a list of files that warrant further inspection.
The hack I saw today was different. The hacker used hexadecimal escaping to hide their tracks. They didn’t just encode hostnames and things that a security analyst would obviously search for. They also encoded individual javascript commands and strings containing HTML element names.
You can use this perl compatible regular expression to search for hex encoded data in your javascript. Again, run this in a shell in the wordpress root installation directory:
grep -rP “(?:\\\\x[A-F0-9]{2}){5}” *
This will search for strings of at least 5 sequential hex encoded digits. You may get some false positives like class-simplepie.php . But again, this will give you a list of files that require closer inspection.
The file that was infected today was wp-includes/js/l10n.js. The attacker had appended hex encoded javascript to it. You can see what a normal file looks like here.
If you’ve been hacked, or suspect you’ve been hacked, drop me an email at mmaunder at gmail. I charge a very reasonable consulting rate and it usually takes 1 to 3 hours to fix the system and harden up permissions to prevent future attacks.