I’m driving through Europe for the next week so am not very available online. Currently in awesome Andorra. So if I’m not very responsive to your WordPress security needs I apologize. However, I have been working on a permanent fix to help with the recent spate of WP hacks and will be making it available as soon as I’m back at work. So apologies for the delay and thanks for your patience.
Category: Security
-
Blogspot security hole lets others view unpublished blog entries
If you use the “new” Blogspot interface, try saving a draft post and then previewing it. You’ll see you’re previewing it using a link that looks something like:
http://example.blogspot.com/b/post-preview?token=<long-encoded-string>&postId=532662776851272&type=POST
One would assume that Blogspot knows you are “you” because you are signed in to Blogspot and it identifies you using a cookie. So it shouldn’t be possible for anyone else on the Net to view your unpublished blog post right? Wrong.
If anyone else sees that link with the token, they simply paste it into their browser and they can view your unpublished blog entry.
I thought that this would present a problem if you’re previewing a blog entry and you click an external link you included in your blog post. This would send your “preview” URL to that external site as a referrer, which means that external site can access your unpublished blog entry. Google seem to have anticipated this and they prevent you from clicking anything on the page by putting a DOM overlay on the preview page.
However, all widgets on the page load. That means if you’re using a Facebook Like button, a stats widget, popular pages widget or any other external javascript widget that logs the current URL (pretty much all of them) then those external sites can access your unpublished blog entry. More importantly anyone who those external sites share the URL with can access your unpublished blog entry.
I thought perhaps if I logged out of Blogspot, that security token would expire and no one would be able to access my unpublished blog entry. Nope. It’s still accessible.
Providing security through the hope that no one will discover a hidden URL in a world where URL sharing has become a deep part of everything we do is not a good design. Blogspot team please fix this. Thanks.
-
A peek into our Space Intelligence Community
I spent the day in a secure area on Buckley Air Force Base called ADF-C or Air Force Data Facility, Colorado. A relative of mine works there and I got an invite to a family day, which I thought was impressive so I thought I’d share some of what I saw.
Walking into ADF-C we had to leave all cellphones, cameras and electronic devices behind and produce two forms of ID to get in. Once inside, there were a wide variety of military personell mixing with civilian contractors. What has surprised me about Buckley on previous visits and again today is the international presence including Canadian and Australian military personell.
The base colonel did an impressive speech on opsec and the importance of the work done on Buckley including the sacrifice families in secure jobs make. “Hi Honey, what did you do at work today?”. “Oh nothing.”. Most families I know, including my own immediate family, talk passionately about our jobs among each other, debate decisions we made, discuss colleagues and work events and so on. Families in secure jobs, including many of my extended family, can never discuss things they work on now or worked on many decades ago. This includes military contractors. Maintaining that discipline is an impressive sacrifice that I don’t think many people appreciate.
Walking into the base, there were many areas we could not access. But they had put together an impressive display for us. The first desk absolutely blew me away. The National Geospatial-Intelligence Agency is based at Buckely. I’ve been using their data for years and recommending it to others and I walked up to the young sergeant behind the desk and literally shook the guys hand and thanked him for the awesome data they make available to the public. Any online business, world-wide, that provides a city or point of interest radius search, uses the NGA’s data and probably dont’ even realize it.
Next up was AGI that makes software to track objects in orbit. The demo they had up was impressive, tracking items in low and medium earth orbits in real-time. The guy was telling me they provide API’s in .NET and Java for developers and as I was listening I looked over my shoulder and totally lost interest because….
The National Security Agency had a booth there. My wife and I immediately headed over and the three people behind the desk were incredibly friendly and forthcoming about their work. But the real treat was that they had a working original enigma encryption machine from WWII. The engima created the strong awareness of the importance of cryptography we have today and it’s one of the main reasons the NSA exists today. Most of the folks behind the desk were mathematicians or worked with, or are married to mathematicians. They have a presence on Buckley and they told us that post 9/11 they diversified beyond Fort Meade (Maryland).
Next up was the National Reconnaissance Office or NRO. These are the guys who actually launch and operate the spy satellites that the NSA and other agencies use. I picked up these cool postcards of a few of the 2010 and 2011 launches they’ve done:
I also chatted to folks from a software division in Lockheed that have designed a 3D walkthrough app that uses real-world photography taken from a reconnaissance aircraft to create a model of an environment. Imagine a Quake walkthrough game of Vegas with actual footage taken at an instant in time of the city. That’s what they had on a demo system. It’s designed to take battlefield intel and provide a walkthrough for folks planning an operation.
We went back to the NSA booth later to play with that enigma some more. It has 3 sets of numbers that are synchronized when two machines are together. Then before a transmission is sent, the sending station will broadcast how much the receiver needs to increment their machine’s numbers by in order to receive the code. The NSA person I spoke to told me that was one of the weaknesses that helped the Polish cryptanalysts (and then Blechley Park) crack the code. That transmission containing the increments always contained no data.
Next up, we took a tour of one of the base radome’s, but on the way I spotted an interesting plaque on a wall in the hallway. It said “Echelon” with a coat of arms and the slogan “Acta Non Verba”. I went back and did a double-take. One the way back I did a triple take. Some amazing history there if you know anything about signals intelligence.
I always thought those Radome’s contained radar systems for local aircraft, considering it’s an Air Force base. But they contain 85 ft diameter satellite dishes that weigh almost 200 tons and rotate at 2 degrees per second when they’re moving. The dome’s are constructed out of a material that seems similar to mylar (main sail material) and are kept at a positive pressure to strengthen them. They can handle winds up to 125mph. If you live in Colorado you’ll know they dot the landscape for hundreds of miles in the Denver and Colorado Springs areas.
I chatted to a bomb tech for way too long about a display they had. Did you know you can fire a rifle into C4 and it won’t detonate? Or the most time consuming explosive to dispose of is sweaty dynamite? My wife chatted to a hostage negotiator. They had a glider and pilot from the civil aviation patrol and we chatted to him for ages about local gliding conditions and riding thermals into Wyoming and back.
They had a cool karate demo at the end of the day – a full contact style I did briefly some time ago called Ken Po. The acrobatics were matrix-like and the base commander broke a pile of 8 bricks and didn’t even flinch when I shook his hand as we were leaving. Cool guy and he seems to be an inspirational leader.
Thanks to all the volunteers at Buckley for spending your Saturday morning letting us civilians peek behind the curtain.
-
Has your WordPress Blog been Hacked? Email me now!
If your WordPress blog has been hacked, please email me. I’m collecting data on intrusion methods and backdoors. If you’ve been hacked, I’ll examine your server free of charge, share what I find with you and will make recommendations on how to repair your site, all at no cost. Please note that I will need “Shell” access to your machine. In other words I’ll need a username and password and will log in via SSH to examine the server that hosts your WordPress blog.
If you’re in dev or ops and have an attack vector you’d like to share, please zip it up and email it to me with as much technical detail as you can.
Email me at mmaunder at gmail.
Thanks!!
-
WordPress Security: Hardening and Malware list removal
I spent some time yesterday reaching out to folks I know to try and get some input on WordPress security, avoiding getting listed as Malware and how to get removed from the Malware list. Rand Fishkin, the founder of SEOMoz and all round SEO God was kind enough to introduce me to Justin Briggs who is an SEO consultant and guru. Justin quickly came back with the following advice:
WordPress is certainly more susceptible to malicious attacks due to its popularity and the large number of sites that can be compromised with an exploit.The best preemptive solution is to keep up on updates and increase security associated with WordPress.Here are two good articles on ways to improve WordPress security.WordPress offers an article on hardening WordPress:http://codex.wordpress.org/Hardening_WordPress And Matt Cutts wrote a few tips on his personal blog:
http://www.mattcutts.com/blog/three-tips-to-protect-your- wordpress-installation/ If a site is compromised, Google will make an effort to get in touch with you. They outlined these details of how they attempt this here:
http://www.google.com/support/webmasters/bin/answer.py? answer=163633#3 They also offer some additional tips:Once a site has been cleaned up, you can send a request to Google:I’ve had a friend’s site who was exploited several months ago. It was a bit of work to get it cleaned up, but the warning was removed relatively quick after submitting the request to Google.I contacted friends who are current and former Google employees but no luck getting in touch with the Malware team. In general it’s hard to connect with folks inside the big G with questions that are usually handled by support teams. [As I’ve been politely told in the past]. 🙂 -
Breaking: Google starts to block hacked WordPress blogs as attack widens
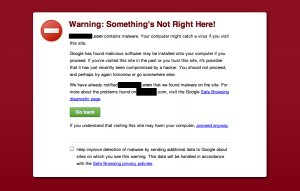
I’ve had two reports in the last 12 hours of WordPress blogs that were compromised via the Timthumb hack being listed as malware by Google. If you try to visit either site, you are confronted with the following:
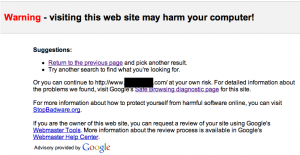
These sites are listed with the warning that “This site may harm your computer” in Google’s search results and Google blocks access to the site with a warning forcing you to manually type the URL into your location bar if you really do want to visit the site:
 One of the site owners sent me the detailed info that Google Webmaster Tools was giving her:
One of the site owners sent me the detailed info that Google Webmaster Tools was giving her: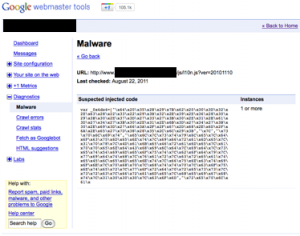 This malicious code is appearing intermittently on this author’s WordPress site. I’ve seen this same pattern recently in blogs I’ve repaired and the way it works is that the site is periodically downloading new PHP code from a remote site run by the attacker and re-injecting it into the wordpress code. That allows the attacker to add, remove and update whatever code he/she is executing on your blog. So they could for example update any spam links every few hours.
This malicious code is appearing intermittently on this author’s WordPress site. I’ve seen this same pattern recently in blogs I’ve repaired and the way it works is that the site is periodically downloading new PHP code from a remote site run by the attacker and re-injecting it into the wordpress code. That allows the attacker to add, remove and update whatever code he/she is executing on your blog. So they could for example update any spam links every few hours.To prevent your site being listed as malware clean it as fast as possible
The fastest way to do this, although it doesn’t gaurantee a complete clean, is the following:
- Remove all old plugins and themes you aren’t using.
- Upgrade all your plugins and themes to the latest versions and make sure none of them use an old version of Timthumb.
- Clean any Timthumb cache directories.
- Upgrade your entire wordpress installation, even if it’s at the latest version. This overwrites all wordpress files.
- Search your directory tree for any remaining suspicious files that contain base64_decode wrapped in an eval() statement or URL encoded data. More info on how to do this search here. Delete any files you find. NOTE: If you don’t find any additional infected files in this step, it’s highly likely that your site is not clean. Every attack that I’ve seen so far using Timthumb gets in by uploading a file into the cache directory and then uploads an additional file into a writeable directory on the blog to ensure continued access once the cache is cleaned. Make sure you find that additional file.
- Make sure the only directory that is writeable in your wordpress installation is wp-content/. Directories like wp-admin and wp-includes should be read only by the web server.
If you are already listed as malware by Google, here is what to do
Clean your site using the above steps. You can find more suggestions on how to clean your site on this page.The fastest way to get your site removed from Google’s malware list is to request a review through Google Webmaster Tools. You can find the help file on requesting a malware review on this page.The process takes about 24 hours to get your site removed. You can find out more about Google’s Malware list and safe browsing report on this page.Potential long term impact of this vulnerability
The fact that I’ve seen the same domain being used by attackers on multiple blogs suggests this attack may be partially or fully automated. The worst case scenario is that we end up with a WordPress botnet with thousands or tens of thousands of servers on high bandwidth links compromised and able to send spam emails or launch a huge DDoS attack.
Keep in mind that most botnets are compromised windows machines on relatively slow home broadband connections. Their uplink speeds are around 512kbps. These WordPress servers are on links that are a minimum of 10 Megabits per second each, so they have plenty of firepower for a coordinated attack. One WordPress server is equal to at least 20 infected PC’s in terms of pure bandwidth firepower.
-
WordPress Security: Please delete old themes and plugins
I was contacted by another site owner who was hacked via vulnerable WordPress themes today. He had updated to the latest non-vulnerable version of his theme, but the WordPress theme installation or update process doesn’t remove, or remind you to remove, old themes that may be vulnerable. So while they encourage you to update everything, old versions are still lurking on your site waiting for an attacker to take advantage of them.
Remember: Delete all old unused themes and plugins.
In this case an attacker once again used an old version of timthumb to install an attack shell called Sniper_SA. The attack shell was Arabic so I’m assuming the attack came from an Arabic country. [The last 3 I’ve seen were english]. This one was base64 encoded inside a PHP eval.
The web host is one of the top 3 WordPress.org hosts on the web. Their default installation is to have your entire WordPress installation writeable by the web server and the server can even write to your home directory under the web root. This opens up all sorts of possibilities for a hacker to gain a remote shell. WordPress hosts, please secure your default WordPress installations so that only directories under wp-content/ are writeable. Also make sure the user’s home directory is not writeable by the web server by default.
-
Two techniques to scan your WordPress installation and check if you're hacked.
I just helped another target of the timthumb.php vulnerability to clean their machine. The method the hacker used to hide their tracks was a little different to what I’ve seen in the past. So I wanted to mention it here and let you know how to scan for it.
As I previously mentioned, the method I’ve seen hackers use to hide their source code is to encode it using base64 encoding and then use base64_decode and eval() in PHP to execute the code at runtime.
You can scan for base64 decoding by getting a shell on your WordPress server and running the following in the root of the WordPress installation directory:
grep -r base64_decode *
Keep in mind that some files that are not hacked will show up, like the newest version of timthumb.php which includes a base64 encoded image. But this is a good starting point to get a list of files that warrant further inspection.
The hack I saw today was different. The hacker used hexadecimal escaping to hide their tracks. They didn’t just encode hostnames and things that a security analyst would obviously search for. They also encoded individual javascript commands and strings containing HTML element names.
You can use this perl compatible regular expression to search for hex encoded data in your javascript. Again, run this in a shell in the wordpress root installation directory:
grep -rP “(?:\\\\x[A-F0-9]{2}){5}” *
This will search for strings of at least 5 sequential hex encoded digits. You may get some false positives like class-simplepie.php . But again, this will give you a list of files that require closer inspection.
The file that was infected today was wp-includes/js/l10n.js. The attacker had appended hex encoded javascript to it. You can see what a normal file looks like here.
If you’ve been hacked, or suspect you’ve been hacked, drop me an email at mmaunder at gmail. I charge a very reasonable consulting rate and it usually takes 1 to 3 hours to fix the system and harden up permissions to prevent future attacks.
-
A secure rewrite of timthumb.php as WordThumb
Update 3 (Final): WordThumb has now been merged into TimThumb and has become TimThumb 2.0. Please head over to the TimThumb site now for updates and to get the code.
Update 2: WordThumb can now take screenshots of websites for you and turn them into thumbnails.
Update 1: Two minor bugs fixed and new minor version released. Thanks guys! You can post bugs directly on this page if you find any more.
I’ve done a full top to bottom rewrite of timthumb and forked the project as WordThumb. You can find it on Google Code with basic instructions on how to use it. Please report any bugs to me at mmaunder at gmail as soon as you can. The code is tested on Ubuntu Linux under Apache and works great.
The only code that is still original timthumb code is the image processing routines. Everything else has been rewritten from scratch. Here are the changes:
- Code is now object oriented PHP and is much more manageable and readable. It will still run just about anywhere.
- Fully backwards compatible with all timthumb’s options.
- Uses a non-web accessible directory as cache for security. By default it uses the system temporary directory. There is a config option to override this.
- All cached files have a .txt extension as an extra precaution.
- Cache cleaning has been rewritten to be faster and only run once a day (user configurable) with no contention between processes.
- ALLOW_EXTERNAL now works as expected. If disabled, you can’t load external files.
- mime type checking is improved. Previously files would be written to a web accessible cache before the mime check step. Now the furthest a non-image will get is a temporary file which fails a mime check and is deleted.
- Previously, the check_cache function created a directory with 777 permissions. That’s removed and we simply use the system temporary directory for everything cache related now.
- Writing images uses file locking now to avoid two processes writing to the same image file and corrupting it.
- We now use temporary files when fetching remote images rather than using the same filename we’re turning into a thumbnail. This avoids another process on a busy server thinking a file is a cached thumbnail and serving an unprocessed image accidentally.
- Fixed browser headers like accept-ranges.
- Improved error reporting.
- Added debug mode with tons of debug messages.
- Debug messages include benchmarking to see where slowdowns occur if any. (It’s very fast!)
- Cleaned up conflicting curl options like CURLOPT_FILE
- Added ability to disable browser caching for debugging
- Added clarity on curl timeout (many sites use php’s default fetching which doesn’t have a timeout)
-
Technical details and scripts of the WordPress Timthumb.php hack
UPDATE: WordThumb has now been merged into TimThumb and has become TimThumb 2.0. Please head over to the TimThumb site now for updates and to get the code.
As I mentioned yesterday my WordPress blog was hacked. The security hole has been picked up by hacker news and from there, The Register, ZDNet, PCWorld, and Geek.com among others. The publicity will hopefully get Theme developers to update timthumb.php or switch to a different thumbnail generator.
I’ve been contacted with requests for detailed info, so I’m going to post the technical details of how my site was hacked along with the scripts that the hacker used to get in. This is targeted at a technical audience.
The server that served you this web page is the one that was hacked. It runs Ubuntu 10.10 with all security updates installed. It is a virtual server hosted by Linode.
I also run the latest version of WordPress.org.
My WordPress root directory was writable, but making it read only would not have prevented the hack.
Timthumb.php in it’s default configuration allows site visitors to load images from a predefined set of remote websites for resizing and serving. Timthumb offers a caching mechanism so that it doesn’t have to continually re-process images. The cache directory lives under the wordpress root and is accessible by visitors to the website.
The ability for a site visitor to load content from a remote website and to make the web server write that remote content to a web accessible directory is the cause of the vulnerability in timthumb.php.
To be clear, timthumb.php does not actually execute any remote malicious code that causes this vulnerability. This was a point of confusion among some commenters in my blog post yesterday. It simply gets a remote file and places it in a web accessible directory.
Timthumb only allows remote content from a small range of websites to be loaded remotely. In it’s default configuration these included Blogger, WordPress.com and other sites that are writeable by the general public.
Timthumb’s verification that remote content was only being loaded by these domains was also broken. You could for example load content from hackersiteblogspot.com or from blogspot.com.hackersite.com.
I’ve submitted a patch that fixes the pattern matching and removed all default public hosting sites from the allowed sites list. The developer has opted to keep a small list in which I’m not in favor of.
In my case the hacker uploaded a script to my cache directory which timthumb.php stores as “external_<md5 hash>.php”. He/she then accessed this script directly in my timthumb cache directory as something like https://markmaunder.com/wp-content/themes/Memoir/scripts/cache/external_md5hash.php
The script uploaded was Alucar shell which is base64 encoded and decodes when it executes. That makes it a little harder to find it using grep or similar tool. You can see the encoded version of Alucar here and the decoded version of Alucar here (without the username and password preamble at the top).
Here’s a screenshot of the UI:
This script which gives a web based shell access was then used to inject base64 code to one of my core wordpress files wp-blog-header.php which lives in the wordpress root directory. The file with injected code looked like this.
The decoded version of this base64 code is this. The code executes whenever a blog page is visited. It fetches a file from a URL and writes it to /tmp. Then it executes the php code that is contained in this file. In my case it simply echo’d some javascript code that would show ads. Here is the code contained in the file in /tmp.
Again, this file is periodically updated with new PHP code, so the attacker could have his way with my server until I found out about it. The code could be altered to instead become a spam system and work it’s way through a long list of spam emails.
The way I tracked this to conclusion was:
- Heard audio on my blog telling me I’d won something.
- Checked Chrome network tools and saw ad content loading and I don’t serve ads.
- Grepped wordpress source and themes for hostname I saw in ad. Nothing.
- Dumped mysql databases on server (all of them) and grepped for hostname. Nothing.
- Confusion reigns.
- Started working my way through nginx (which is my front end proxy to apache) and apache access and error logs.
- Spotted lines in apache error log like this: “[Mon Aug 01 11:09:12 2011] [error] [client 127.0.0.1] PHP Warning: file_get_contents(http://blogger.com.zoha.vn/db/load.php): failed to open stream: HTTP request failed! in /usr/local/markmaunder/wp-content/themes/Memoir/timthumb.php on line 675”
- Checked timthumb’s cache directory and found Alucar.
- Realized base64 encoding is why I didn’t find anything with grep.
- Regrepped wordpress source and database and found injection in wp-blog-header.php
- Decoded base64 stuff and played with Alucar
- Found tmp file in /tmp
- Cleaned everything and fixed permissions. Ran chkrootkit and other utils on machine to see if anything else was compromised. Changed passwords, etc.